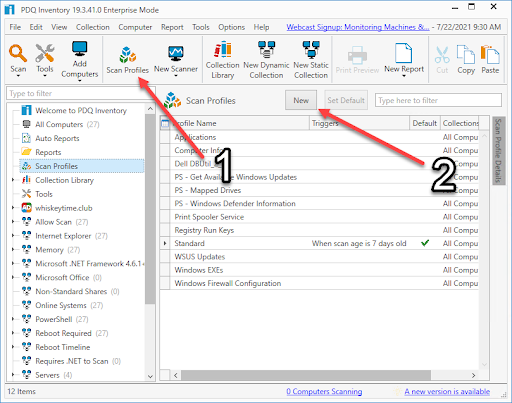
PowerShell "Automation" for larger infrastructure. · Issue #165 · logpresso/CVE-2021-44228-Scanner · GitHub
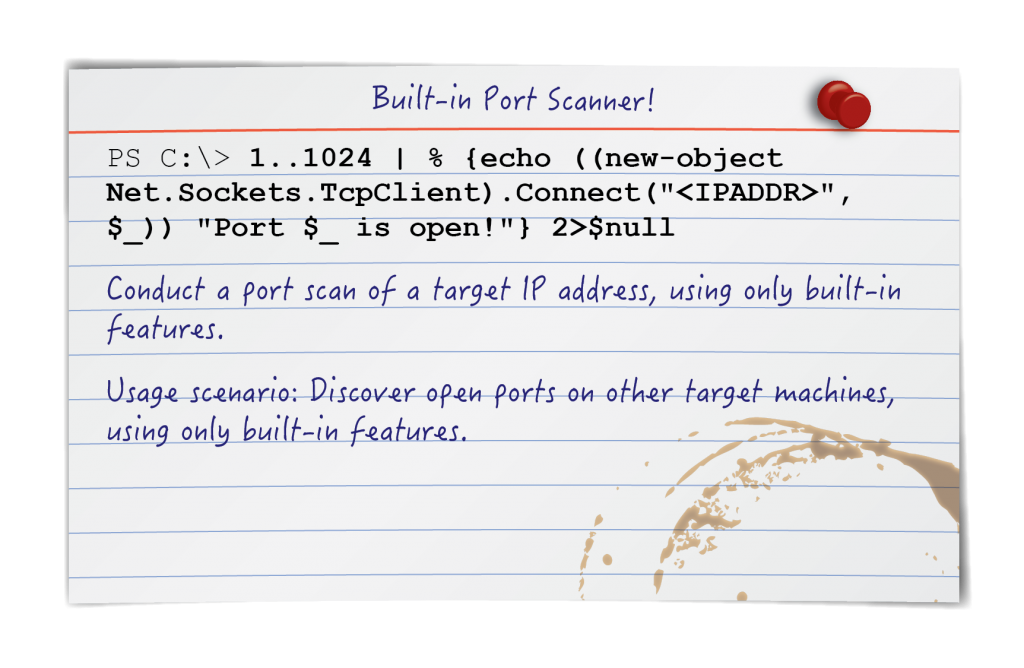
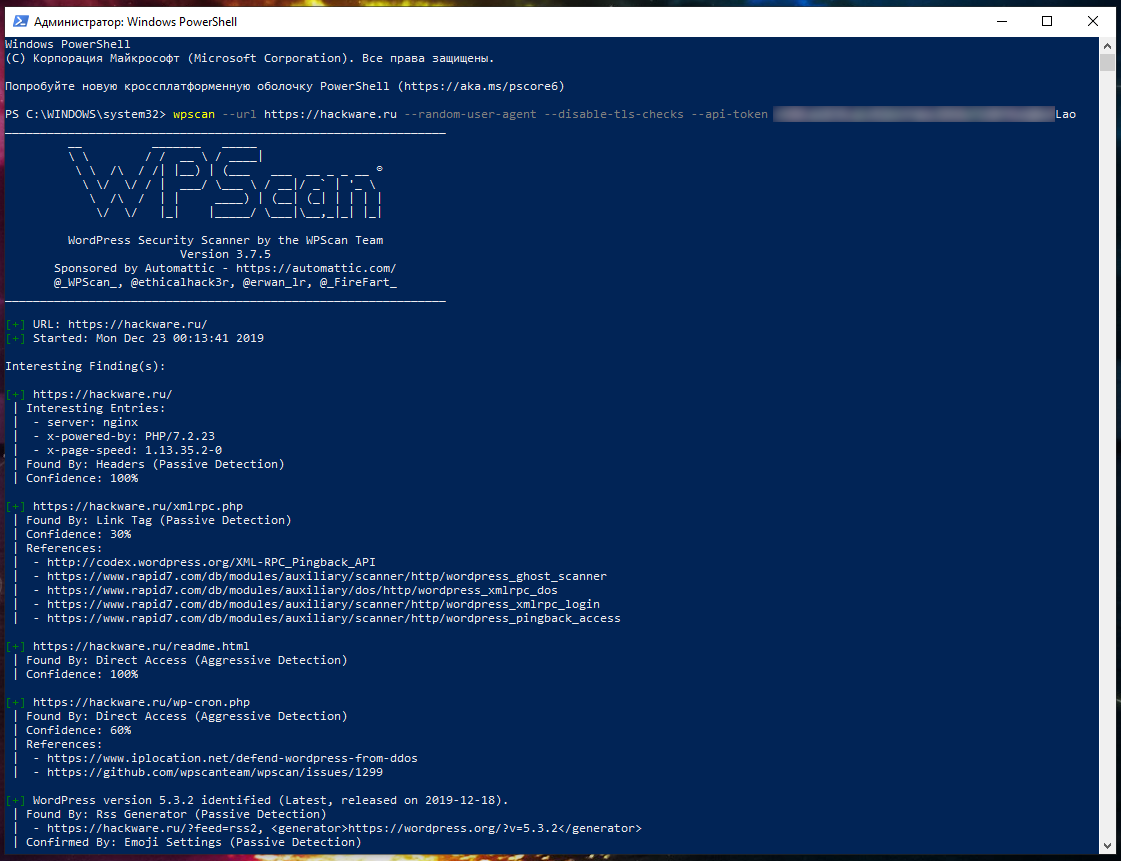
SANS Penetration Testing | Pen Test Poster: "White Board" - PowerShell - Built-in Port Scanner! | SANS Institute
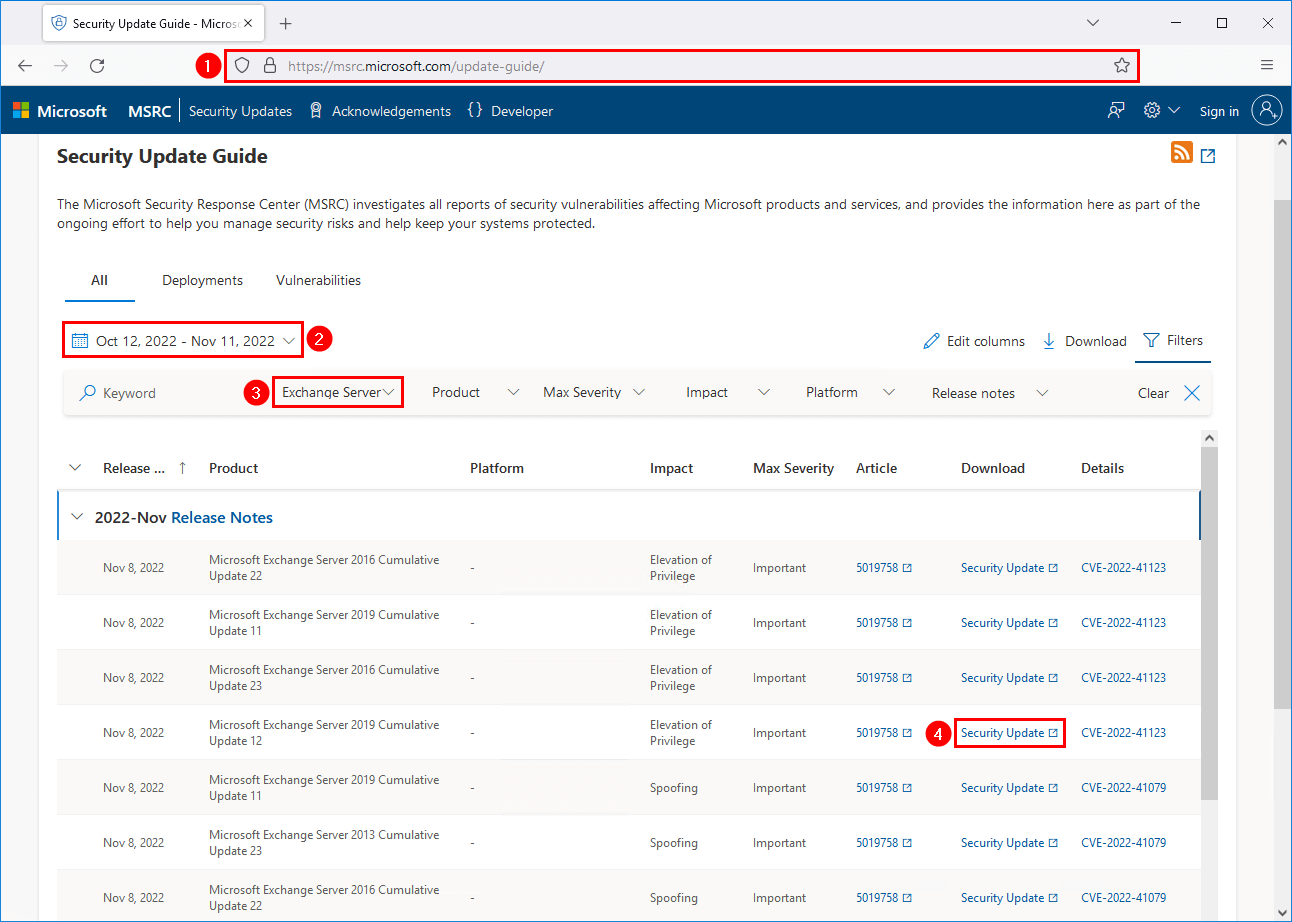
Threat Assessment: Active Exploitation of Four Zero-Day Vulnerabilities in Microsoft Exchange Server
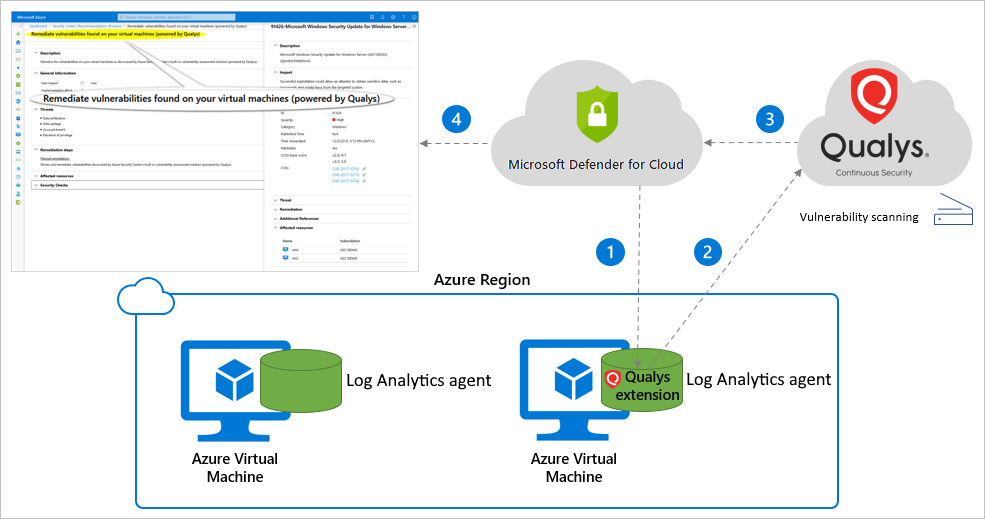
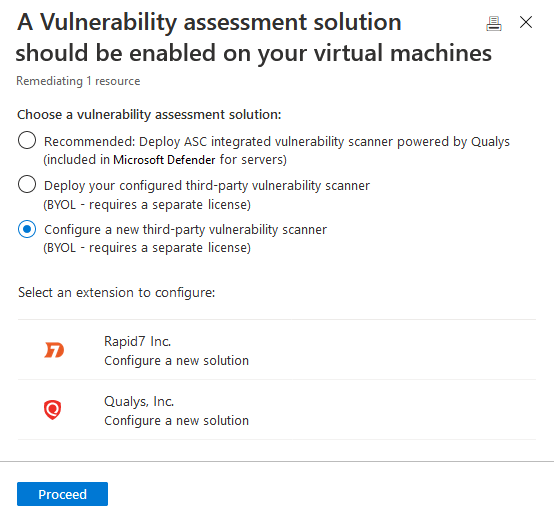
Defender for Cloud's integrated vulnerability assessment solution for Azure, hybrid, and multicloud machines | Microsoft Docs
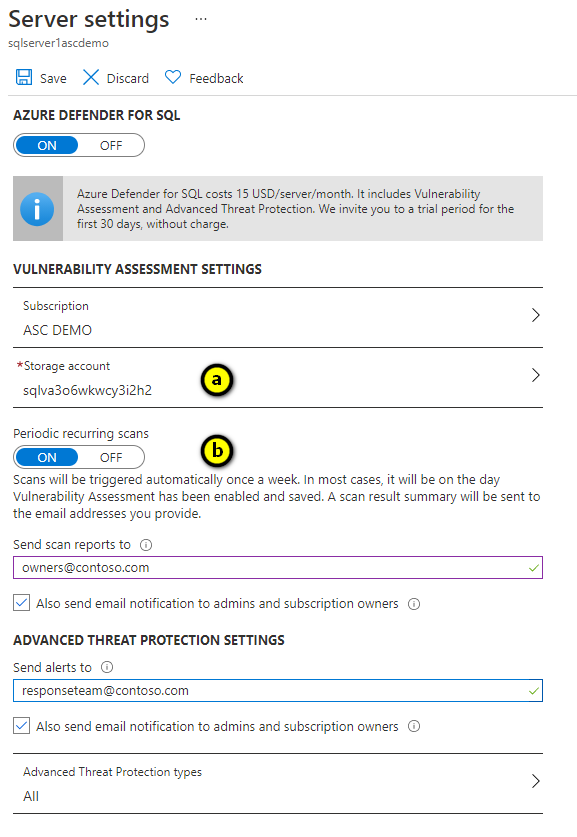
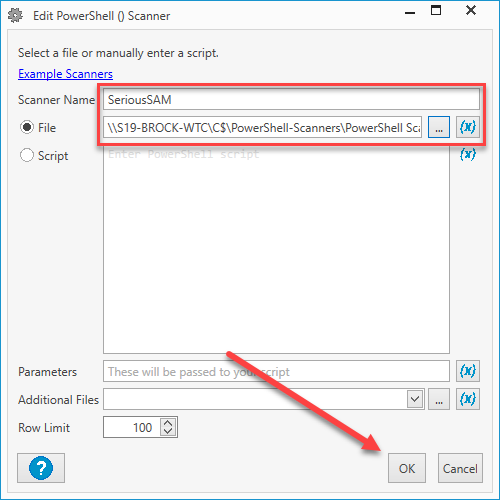
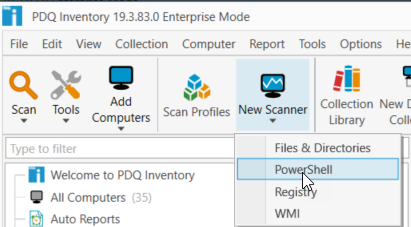
SQL vulnerability assessment - Azure SQL Database & SQL Managed Instance & Azure Synapse Analytics | Microsoft Docs

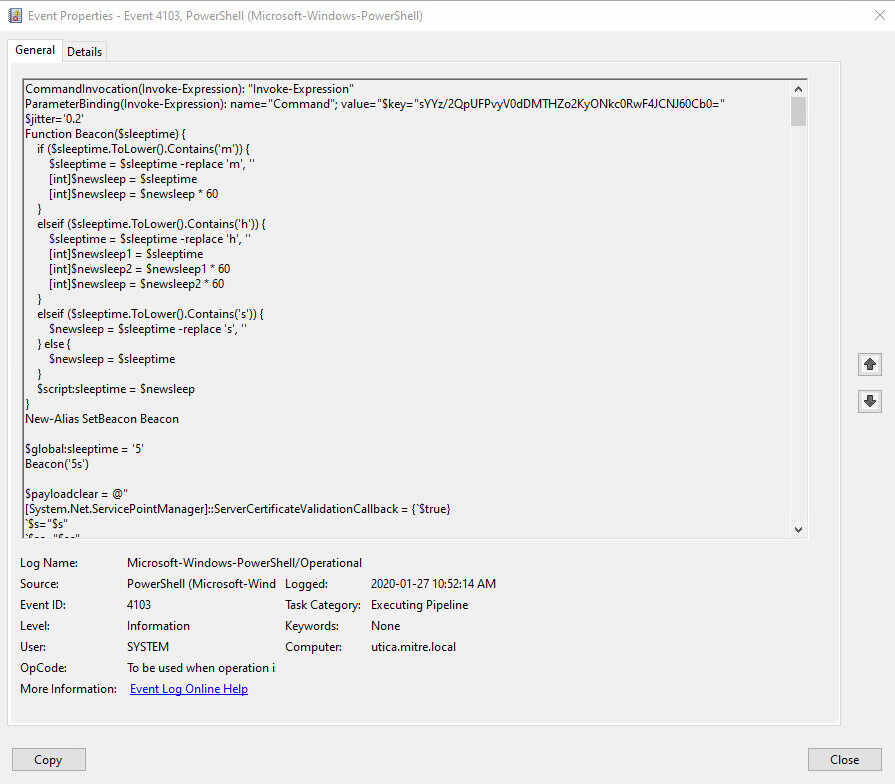
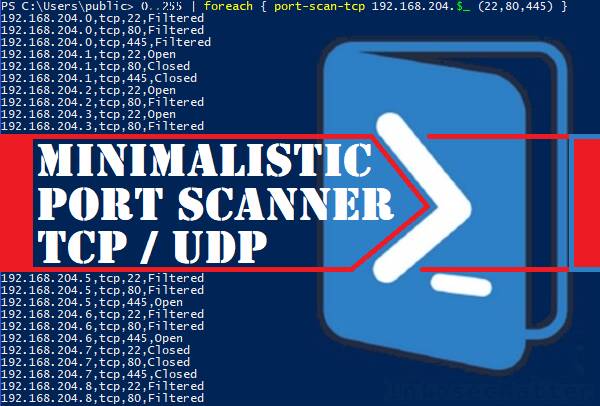
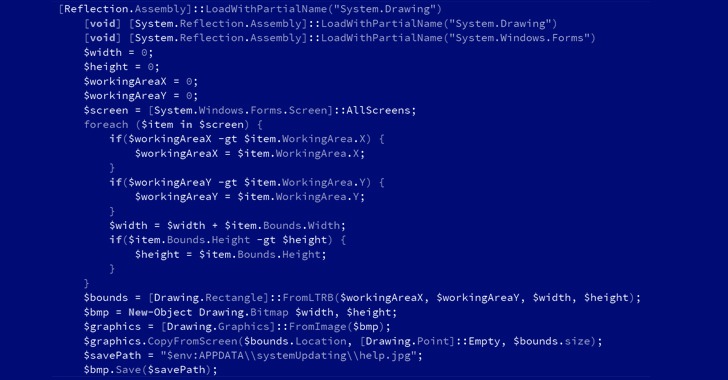
Attack and Defense Around PowerShell Event Logging - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.

Attack and Defense Around PowerShell Event Logging - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.





.jpg)